Game Over: Hackers Embed Malware in Steam Game to Steal Gamers’ Passwords!
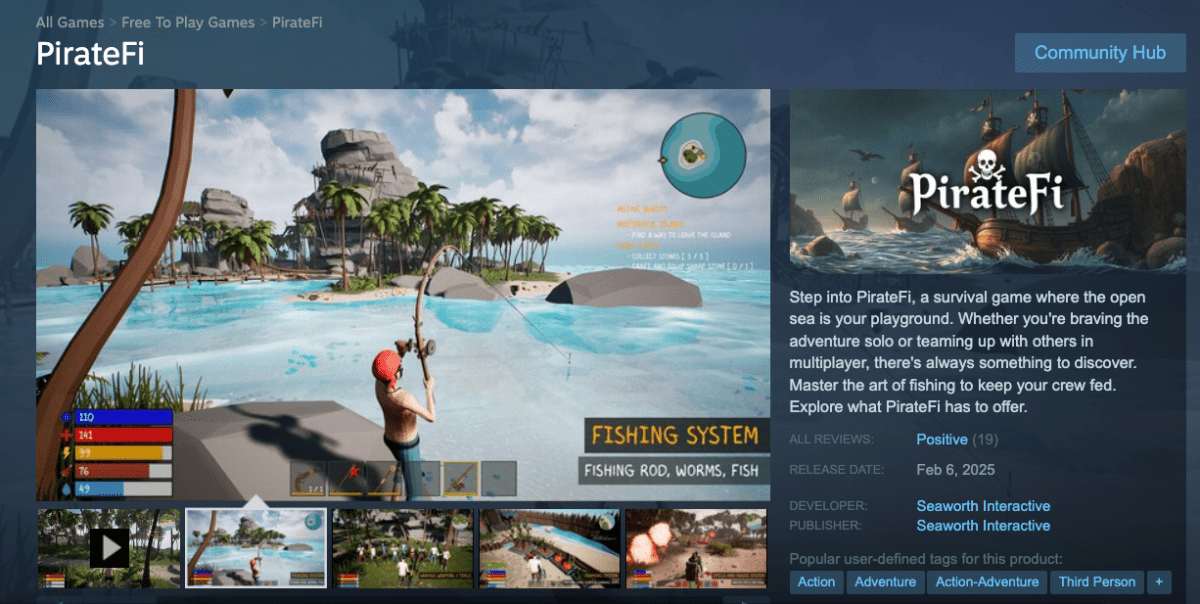
In a recent incident that highlights the growing concerns over online gaming security, Valve took swift action to remove a game from its popular platform, Steam, due to malware infiltration. The game, named PirateFI, was found to contain malicious software designed to steal sensitive user information.
The Discovery of Malware in PirateFI
Security researchers have conducted an in-depth analysis of the malware embedded in PirateFI. Marius Genheimer, a researcher at Falcon Team, provided insights to TechCrunch, stating that the malware was likely part of a broader strategy to distribute a harmful payload known as Vidar.
Understanding the Threat
Genheimer noted, “We suspect that PirateFI was just one of multiple tactics used to distribute Vidar payloads en masse.” He emphasized that the game was likely never legitimate and was specifically designed to spread malware.
How the Malware Operated
Research revealed that PirateFI was created by modifying a game template called Easy Survival RPG, a game development tool that costs between $399 and $1,099 to license. This method allowed hackers to deploy a functional game with minimal effort.
Capabilities of Vidar Infostealer
The Vidar malware is notorious for its ability to steal various types of data from infected computers, including:
- Password information from web browsers
- Session cookies for unauthorized access
- Web browser history
- Cryptocurrency wallet details
- Screenshots and two-factor authentication codes
- Other sensitive files
Since its discovery in 2018, Vidar has been implicated in multiple hacking campaigns, including efforts to steal credentials from Booking.com and deploying ransomware. According to the Health Sector Cybersecurity Coordination Center (HC3), Vidar has become one of the most successful infostealers in recent years.
Challenges in Identifying the Perpetrators
Infostealers like Vidar are often sold through a malware-as-a-service model, making it easier for even inexperienced hackers to utilize them. This widespread availability complicates efforts to trace the origins of malicious software like PirateFI.
Research Findings and Developer Anonymity
Genheimer and his team analyzed multiple samples of the malware, discovering similarities across various sources, including VirusTotal and SteamDB. Despite these findings, Valve has not commented on the matter.
The developers behind PirateFI, identified as Seaworth Interactive, lack an online presence, and their social media account was removed shortly after the incident. Attempts to reach out for comments went unanswered.
Stay Informed on Cybersecurity
For more updates on cybersecurity in gaming, consider following CNET’s gaming section and stay vigilant against potential threats.
If you have additional information regarding this malware or other gaming-related hacks, please reach out securely through TechCrunch.