Justice Department Unveils Charges Against Chinese Hackers-for-Hire Tied to Treasury Breach
The recent announcement from the Department of Justice (DOJ) has shed light on a significant cybercrime case involving Chinese government-linked hackers. Twelve individuals have been charged with hacking more than 100 American organizations, including high-profile targets like the U.S. Treasury, over a span of ten years.
Details of the Charges Against Chinese Hackers
According to a senior DOJ official, the accused hackers played a pivotal role in China’s hacker-for-hire ecosystem. The charges include contract hackers and officials from Chinese law enforcement who allegedly targeted organizations both in the United States and globally, aiming to suppress free speech and religious freedoms.
Involvement of APT27 Hackers
The indictment specifically mentions two individuals, Yin Kecheng and Zhou Shuai, who are associated with the Chinese government-backed hacking group known as APT27 or Silk Typhoon. These hackers are accused of conducting multi-year, for-profit computer intrusion campaigns since 2013.
- The operations allowed them to steal sensitive data from various organizations.
- Stolen information was reportedly sold to third parties, some connected to the Chinese government.
Exploitation of Security Flaws
The DOJ’s unsealed indictment reveals that Yin and Zhou exploited numerous security vulnerabilities in widely used enterprise software. Recent research from Microsoft confirms that the hackers took advantage of flaws in:
- Microsoft Exchange
- Palo Alto Networks firewalls
- Citrix NetScaler appliances
- Ivanti Pulse Connect Secure appliances
Targets of the Cyber Attacks
The targeted organizations included:
- U.S.-based technology firms
- Think tanks
- Law firms
- Defense contractors
- Local governments
- Healthcare systems
- Universities
Yin has also been linked to a significant hack of the U.S. Treasury that occurred in December 2024. Following an investigation, the Treasury Department sanctioned him in February, connecting him to China’s Ministry of State Security (MSS).
Seizure of Hacking Infrastructure
The FBI has reportedly seized the virtual private servers and other infrastructure utilized by Yin to execute the attack on the U.S. Treasury.
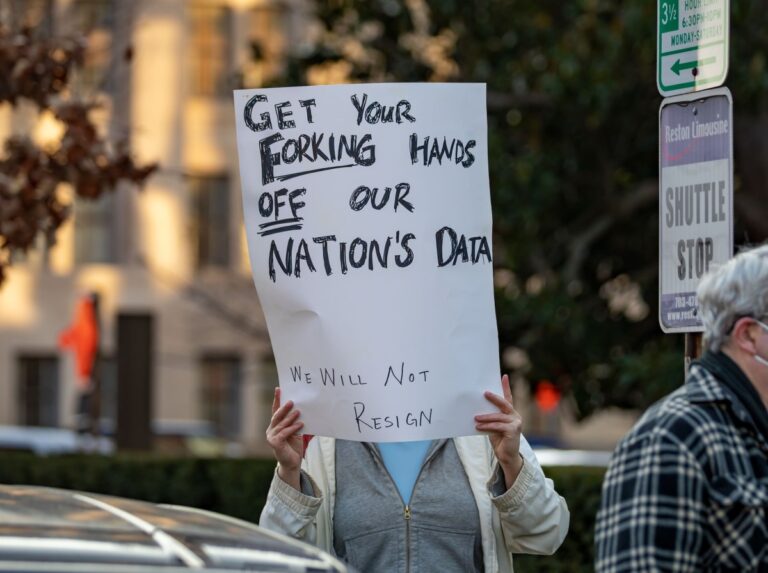
Charges Against I-Soon Employees
In a related development, the DOJ has charged eight employees of the Chinese hacking contractor I-Soon, including its CEO and COO. These individuals, along with two officers from China’s Ministry of Public Security, are accused of running a substantial hacking campaign from 2016 to 2023, generating tens of millions of dollars.
- I-Soon employees are alleged to have conducted hacks at the request of Chinese security agencies.
- They also engaged in intrusions independently, selling the stolen data to the Chinese government.
The organizations targeted included a religious group critical of the Chinese government and several U.S. news agencies promoting religious freedoms.
Rewards for Information
The defendants remain at large, prompting the U.S. Department of State’s Rewards for Justice program to offer rewards for information leading to their apprehension:
- Up to $10 million for information on any I-Soon employees.
- Up to $2 million for details that lead to the arrest and conviction of Yin and Zhou.
For more information on cybersecurity threats and protective measures, visit CISA.