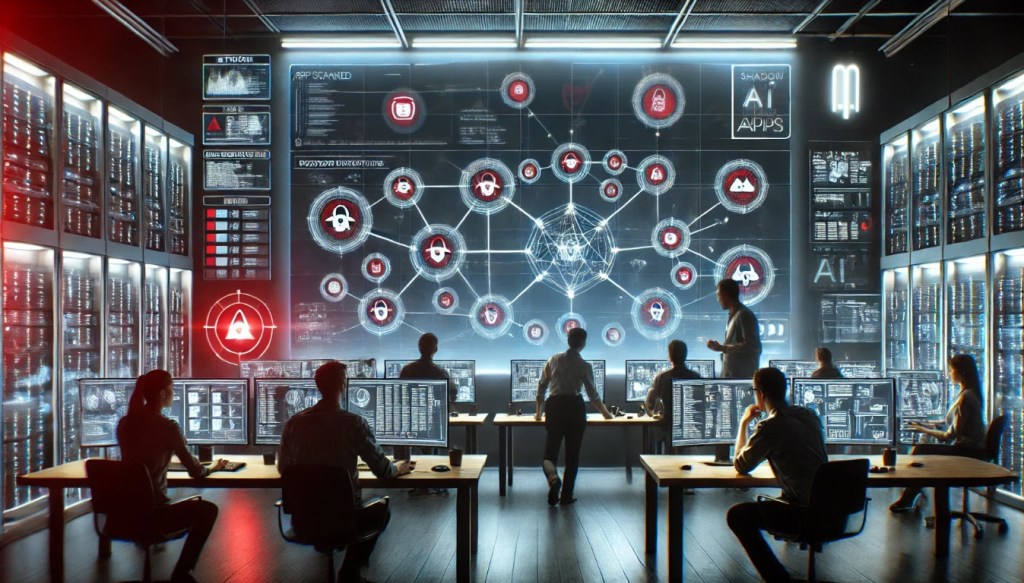
Shadow AI: Safeguarding Your Security Against Unapproved AI Apps – Essential Strategies for Protection
In today’s digital landscape, shadow AI applications pose a significant threat to organizational security. Security leaders and Chief Information Security Officers (CISOs) are increasingly aware of how these unauthorized tools can infiltrate their networks, often without detection.
The Rise of Shadow AI Applications
Over the past year, security experts have noticed a troubling increase in the use of shadow AI applications within corporate environments. These tools, often developed and implemented without the consent of IT departments, can lead to serious vulnerabilities.
What Are Shadow AI Applications?
- Unauthorized Use: Shadow AI applications refer to AI tools that employees use without formal approval from IT.
- Potential Risks: These applications can expose sensitive data and create entry points for cyberattacks.
- Rapid Growth: The rise of remote work has accelerated the adoption of these shadow tools.
Understanding the Impact on Network Security
As more employees turn to shadow AI for efficiency, the potential risks to network security enhance. Here are some key impacts:
- Data Breaches: Unauthorized applications can lead to unintentional data leaks.
- Compliance Issues: Companies may struggle to meet regulatory standards when using unapproved tools.
- Increased Attack Surface: Each new application can introduce additional vulnerabilities to the network.
Strategies for Mitigating Risks
To combat the challenges posed by shadow AI applications, security leaders can implement several effective strategies:
- Establish Clear Policies: Create guidelines for the use of AI tools within the organization.
- Conduct Regular Audits: Regularly review applications being used across the network.
- Promote Awareness: Educate employees about the risks associated with shadow AI.
By addressing the issue head-on, organizations can better protect their networks and sensitive information.
Conclusion
The emergence of shadow AI applications is a pressing concern for security leaders and CISOs. By understanding the risks and implementing effective policies, organizations can safeguard their networks against these unauthorized tools. For more information on enhancing your cybersecurity strategy, visit Cybersecurity.gov or check out our internal resources on cybersecurity best practices.